By Sam Bocetta
230,000.
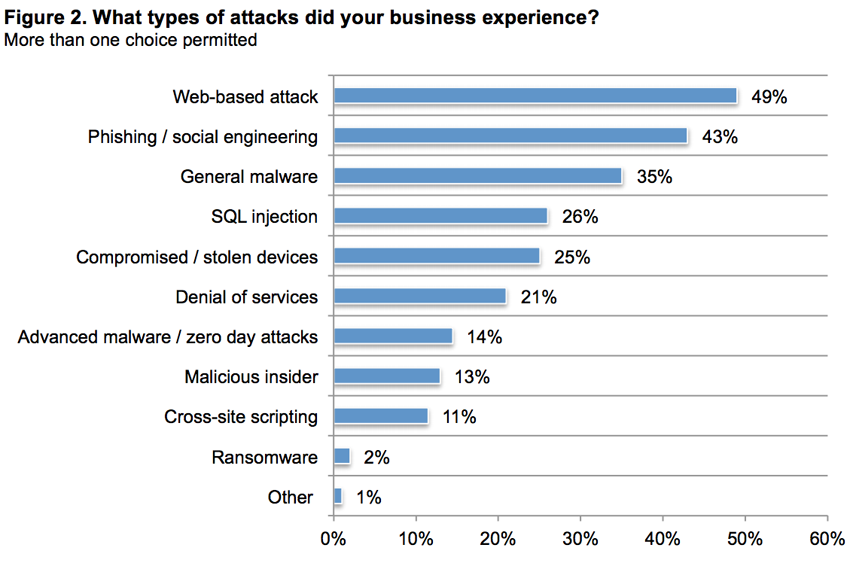
That’s the number of new malware samples that are produced each and every day. In 2017, 43 percent of companies reported cyber attacks or security breaches, totaling more than 160,000 separate incidents. Since such crimes often go unreported, security experts estimate that the real number is more than double that amount and continues to climb.
It isn’t as though organizations and the public aren’t aware of the potential for data breaches. Even high-profile bloggers and tech writers aren’t immune to hackers.
When tech-savvy experts aren’t safe in cyberspace, how can business owners with limited financial and IT resources protect themselves?
Seventy percent of business owners now feel that cyber threats pose a greater danger than ever before. Where are these threats coming from, and what can you do to minimize them?\
What are the biggest threats to cyber security?
As a small-to-medium business (SMB) owner, you may think that you’re an unlikely target for cyber crime. After all, most criminals are after money, and you’re a small fish in a pretty big pond.
However, nearly half of all cyber attacks happen to small companies. The remainder of data leaks and breaches are often due to carelessness and human error. This makes such incidents nearly 100 percent preventable, in theory.
Cyber crime: shocking statistics for SMBs
For every story about hacking and cyber crime that makes the news, thousands never propagate beyond local media—if they’re reported at all. That may be helpful to organizations from a PR standpoint, but it provides a false picture of the scope and ultimate cost of cyber crime.
Here are a few statistics that are guaranteed to give you a wake up call:
- Close to seven billion records were exposed in the first three quarters of 2017; according to OTA, up to 97 percent of them could have been avoided using basic security protocols.
- Only 14 percent of small business owners rank their cybersecurity as effective.
- Sixty percent of small companies go out of business within six months of a cyber attack.
- Cyber crimes are expected to cost $6 trillion dollars annually by 2021. That’s more than double the cost from 2015.
- One-third of all phishing emails are opened by the recipient. Kapersky reports that its Anti-Phishing System was triggered a total of 246,231,645 in 2017, an increase of 91 million over the previous year.
- It take most companies an average of 206 days to notice a data breach.
- According to the FBI, there are 4,000 ransomware attacks launched every day; on average, they hit a business every 14 seconds.
The first step toward preventing attacks and accidental data loss is learning what type of threats are out there. Then, you can put measures in place to stop your company from becoming another statistic.
According to Security Magazine, 93% of data breaches can be traced back to an employee. That makes human error the number one source of trouble.
Rounding out the top security threats are:
- Ransomware – this includes holding data hostage for profit through malware.
- Uneven or incomplete cybersecurity protection – spotty or haphazard security leaves too many vulnerabilities exposed; all security measures should be enterprise-wide.
- Software subversion – hackers love finding and exploiting software vulnerabilities and security flaws.
- Distributed denial of service (DDoS) attacks – whether the point is to overwhelm corporate resources for kicks or cover other breaches-in-progress, this old trick continues to plague website owners and admins.
You could hire a cybersecurity firm to perform an audit or outsource your protection. However, the best prevention lies closer to home.
Best practices: five ways to protect your small business
Last year’s big news stories about ransomware attacks and data leaks have made the public more aware than ever of the need to step up security. Even personal computers and mobile devices are being encrypted by their owners. Although many companies are implementing stricter security measures, too few are going far enough.
Here are five things that you can do, starting today.
1. Implement strict access policies.
Known as a Principle of Least Privilege, this limits employee access to only information and systems necessary to perform their job. You can also create and enforce rules regarding the use of personal devices for work and stop work devices from being used at home.
2. Create a comprehensive employee training program.
Whether by negligence, carelessness, or intentional malfeasance, employees are one of the main causes of security breaches. Since most happen by accident and are due to lack of training and education, they’re easily avoidable.
- Create a sense of urgency that helps all staff members feel invested in data security.
- Train employees on the basics of cybersecurity, such as password creation, data encryption, and how to recognize malware or phishing attempts.
- Create and implement uniform policies regarding data storage and backups.
3. Abide by the Financial Industry Regulatory Authority (FINRA) cybersecurity checklist.
This downloadable checklist was created especially for SMB owners in an effort to assist smaller firms with creating effective cyber security protocols.
It covers four key areas:
- Identifying and assessing risk
- Detecting system and data breaches
- Planning a response to leaks or breaches
- Creating an asset and data recovery plan
4. Use strong passwords and change them frequently.
Using weak passwords is like leaving your front door unlocked. Newer platforms aid with this by adding password creation monitoring that provides feedback regarding password strength.
A strong password should be at least 12 characters long and contain a mix of uppercase and lowercase letters, numbers, and at least one symbol. There should be a separate password for each device and account, and they should be changed every three months, minimum.
Since so many of us have multiple devices and accounts, deploying a password manager to generate and track them is imperative. This handy little software package will do better than your brain ever could at the task of remembering and inserting the appropriate username and password for any of the dozens of entries you encounter in daily life. It’s more convenient and more secure.
5. Protect your data.
Shore up your overall security by using anti-malware and anti-virus software and keeping it updated. Other technological security aids include data encryption through secure socket layer (SSL) certificates, installing a virtual private network, and using a dedicated server to host your website.
The wrap-up
Recent reporting by the Online Trust Alliance (OTA) determined that 2017 was the the second-worst year for cyber crime in history (2013 took the title solely due to that massive attack on Yahoo). It was even christened “The Year of the Data Breach.”
Things have only continued to worsen since those stats were revealed.
We’ll never completely eradicate cyber crime. However, you can minimize your exposure by investing in proper security, keeping it updated, and ensuring that employees are properly trained in best practices that keep personal and customer data safe. Following security protocols—and making sure your staff does the same—will go a long way toward protecting your sensitive data.
Sam Bocetta is a freelance journalist specializing in U.S. diplomacy and national security, with emphases on technology trends in cyberwarfare, cyberdefense, and cryptography.
